Quick Reference Table
| Detail | Information |
| Full Name | DoD Instruction 5200.48, Controlled Unclassified Information |
| Published | March 6, 2020 |
| Who Signed It | Joseph D.Kernan, Under Secretary of Defense for Security and Intelligence |
| What It Replaced | DoD Manual 5200.01, Volume 4 (February 2012) |
| Parent Authority | Executive Order 13556 (signed 2010), 32 CFR Part 2002 |
| Federal Overseer | NARA — National Archives and Records Administration |
| Applies To | All military branches, defense agencies, contractors, and anyone handling DoD information |
| Key Related Rule | DFARS 252.204-7012 for contractors |
| Tech Standard | NIST SP 800-171 |
| Penalty for Violation | Administrative, civil, or criminal sanctions |
The Simple Answer First
Let’s get straight to it.
The DoD instruction that implements the DoD CUI Program is DoDI 5200.48, officially titled Controlled Unclassified Information (CUI).
That’s the answer you’ll see on every military training exam and compliance checklist. But if you stop there, you’re missing the full picture. There’s a deeper story behind why this instruction exists, what it actually requires, and why getting it wrong can cost someone their contract — or even land them in serious legal trouble.
Let’s walk through all of it, step by step.
See also “Can You Use a Vanilla Gift Card on Amazon? The Complete, Honest Guide“
First, What Even Is CUI?
Imagine you’re a contractor working on blueprints for a Navy vessel. The documents aren’t stamped Top Secret. They aren’t locked in a vault. But they’re absolutely not something you’d want floating around the internet either.
That’s exactly what CUI is.
CUI stands for Controlled Unclassified Information. It’s government-owned or government-related information that isn’t classified — but still needs careful protection. Think of it as sensitive but not secret. It covers things like privacy records, law enforcement data, technical defense information, export-controlled material, and much more.
Before the CUI program came along, different agencies used their own labels for this kind of material. You had For Official Use Only (FOUO), Sensitive But Unclassified (SBU), Law Enforcement Sensitive (LES), and dozens of others. The chaos was real. One agency’s “sensitive” looked nothing like another agency’s “sensitive.” Sharing became messy, and security gaps opened up.
The CUI program was born to fix that mess.
How It All Started: The Origin Story
Back in 2004, a study inside the Department of Homeland Security identified over 140 different types of unclassified information labels scattered across the federal government. That number alone tells you how badly things needed to be cleaned up.
Years of work followed. Then, in November 2010, President Obama signed Executive Order 13556. That order created a single, government-wide program for handling this kind of sensitive-but-unclassified data. It gave NARA — the National Archives and Records Administration — the job of running it.
NARA didn’t work alone. It used its Information Security Oversight Office (ISOO) to build out the program. By September 2016, NARA published the rules in 32 CFR Part 2002, a detailed set of regulations that every federal agency had to follow.
But here’s the thing. The DoD is massive. It has its own systems, its own contractors, its own complexity. General federal rules needed a DoD-specific translation.Thus, the Office of the Under Secretary of Defense for Intelligence and Security started working.
On March 6, 2020, they released DoDI 5200.48.
What DoDI 5200.48 Actually Does
Think of DoDI 5200.48 as the DoD’s official rulebook for CUI. It takes the government-wide policy and makes it specific to the military and defense world.
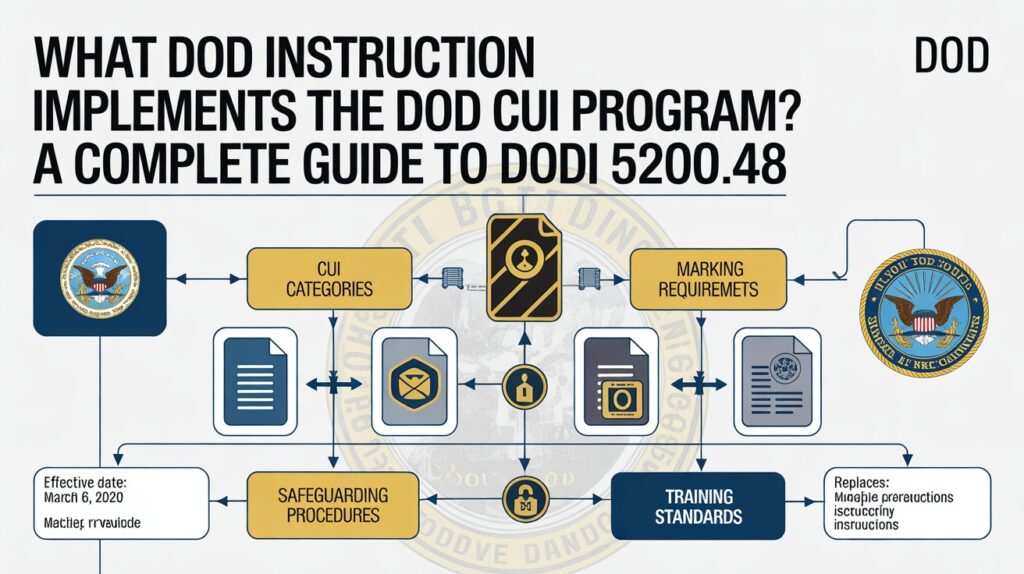
The instruction does three big things. First, it sets the policy — the what and why. Second, it assigns responsibilities — the who. Third, it prescribes procedures — the how.
It also did something particularly important: it created the official DoD CUI Registry. This registry is essentially a catalog of every category of information that counts as CUI within the DoD. Think of it like a library index — if your information matches something in that index, it’s CUI, and the rules apply.
The Chain of Command Behind CUI
This is something that many people find surprising. DoDI 5200.48 didn’t pop out of nowhere. It sits at the bottom of a legal chain that goes all the way up to the White House.
The chain looks like this:
- Executive Order 13556 — The presidential order that started everything in 2010
- 32 CFR Part 2002 — The NARA regulation that built out the program’s rules
- DoDI 5200.48 — The DoD’s specific implementation of those rules (published 2020)
- DFARS 252.204-7012 — The contract clause that makes CUI rules legally binding on contractors
- NIST SP 800-171 — The technical cybersecurity standard contractors must follow
Each layer depends on the one above it. You can’t fully understand DoDI 5200.48 without knowing where it came from.
Who Has to Follow DoDI 5200.48?
The short answer: a lot of people.
The instruction covers the entire Office of the Secretary of Defense, all military departments (Army, Navy, Air Force, Marines, Space Force), the Joint Chiefs of Staff, all Combatant Commands, every defense agency, and all defense field activities. That’s just the government side.
On the contractor side, if your company holds a DoD contract that includes CUI — and the contract includes the DFARS 252.204-7012 clause — you’re in. It doesn’t matter if you’re a massive defense prime or a small business writing software for a base. If you handle covered defense information, the rules apply to you.
One important note: only the government gets to decide what counts as CUI. A contractor can’t look at a document and decide on their own that it’s CUI. The government must identify it through contract language, markings, or explicit guidance. Most people are unaware of how important this is.
CUI Basic vs. CUI Specified — A Key Distinction
Not all CUI is created equal. DoDI 5200.48 (and NARA’s overall framework) recognizes two types.
CUI Basic is the standard type. There’s no specific law telling you exactly how to handle it — beyond the baseline rules. If your information falls into a CUI category but doesn’t have special statutory protections attached, it’s CUI Basic. The protection standard for CUI Basic is NIST SP 800-171.
A practical example: a defense subcontractor working with engineering specs for a naval drone. The data isn’t classified. It isn’t covered by ITAR. But it’s sensitive and tied to national security. That’s CUI Basic.
CUI Specified is the more intense version. Here, a specific law, regulation, or government policy spells out exactly how the information must be handled. It often comes with tighter restrictions on who can see it and stricter controls on sharing.
A clear example of CUI Specified is Naval Nuclear Propulsion Information (NNPI) — data related to nuclear-powered Navy ships. There are very specific legal rules about who touches that material.
The NARA CUI Registry lists 125 total CUI categories organized into more than 20 groupings. Reading through the Registry helps you understand exactly what kind of CUI you’re dealing with.
The Marking Rules: How CUI Looks on Paper
One of the most practical parts of DoDI 5200.48 covers how CUI must be marked on documents.
At minimum, every page of a CUI document must carry the letters “CUI” in a banner at the top and in the footer at the bottom. That’s it for basic page marking. Simple but mandatory.
The instruction also requires a CUI Designation Indicator Block. This block typically appears on the first page and includes:
- The line “Controlled by” followed by the DoD component responsible
- The line identifying the originating office
- The specific CUI category or categories present
- Any distribution statement or Limited Dissemination Controls
- A contact phone number or office mailbox for the originating component
One thing DoDI 5200.48 makes clear: you do NOT add the letter “U” (for Unclassified) next to “CUI” on banners and footers. CUI is already unclassified by definition. Adding “U” would actually be incorrect under the current DoD marking system.
The instruction also clarified that FOUO markings are gone on new documents. “For Official Use Only” has been replaced by the CUI system across the board.
Handling, Sharing, and Storage
The instruction promotes information sharing — but not without limits.
CUI can be shared with anyone who has a lawful government purpose for accessing it. Notice that’s different from classified information, where you need a specific “need-to-know.” With CUI Basic, if you have a lawful reason tied to your government work, you generally have access.
However, CUI Specified may require additional showing before someone can access it.
In terms of physical handling, CUI can travel by first-class mail, parcel post, or bulk shipments. Electronically, it can move through approved secure systems or encrypted email. The key word throughout is “approved.” Personal email accounts and unsecured systems are off the table.
For digital environments, systems that store, process, or transmit CUI must meet the security controls in NIST SP 800-171. That’s 110 specific controls across 14 security families. Everything from access control to incident response to physical protection falls under this standard.
Destruction: Getting Rid of CUI the Right Way
When CUI has served its purpose, you can’t just delete the file and call it a day.
DoDI 5200.48 is very specific. When destroying CUI — paper or digital — it must be made completely unreadable, indecipherable, and irrecoverable. For paper, that means cross-cut shredding or burning. For digital media, it means methods aligned with NIST SP 800-88 media sanitization guidelines.
The goal is simple: no one should ever be able to reconstruct the information, even in pieces.
Before destruction, CUI documents must be formally reviewed and approved for disposition. This isn’t a casual process. It follows the DoD’s records management requirements under Title 44 of the U.S. Code.
Decontrolling CUI: When It’s No Longer Sensitive
CUI doesn’t stay CUI forever. When the information no longer requires protection, it must be decontrolled.
There’s no automatic timer on CUI unless a specific law requires it. Decontrol happens when the reason for protection no longer exists. Once decontrolled, the government notifies all known holders of the information so they can remove CUI markings.
One thing the instruction is very clear about: you cannot use CUI designation to hide embarrassing information, cover up government mistakes, block competition, or suppress legal violations. CUI is a protection tool, not a secrecy weapon.
The Role of Contractors and CMMC
For companies in the Defense Industrial Base, DoDI 5200.48 connects directly to CMMC — the Cybersecurity Maturity Model Certification.
CMMC is the DoD’s system for verifying that defense contractors actually protect CUI the way they’re supposed to. It was formally rolled out to ensure the rules on paper translate into real-world protection across the supply chain — all the way down to subcontractors.
Under CMMC 2.0, contractors handling CUI must achieve Level 2 certification, which maps directly to NIST SP 800-171. That means a third-party assessment verifying that all 110 controls are in place. Fail the assessment, and you can’t compete for DoD contracts. For thousands of small businesses, that’s an existential threat.
The connection between DoDI 5200.48 and CMMC is tight. The instruction defines what CUI is and how to handle it. CMMC verifies that the handling is actually happening.
Common Mistakes People Make
Even experienced organizations trip up on CUI compliance. Here are the most common problems:
Mislabeling or forgetting banner markings is the most frequent audit failure. The “CUI” banner at the top and bottom of every page is required — not optional.
Storing CUI on personal devices or unauthorized cloud services is prohibited. This happens more than people admit, often accidentally.
Treating everything as CUI is also a mistake. A company budget, for example, is not CUI unless it belongs to a federal agency. Over-marking wastes resources and creates confusion.
Assuming silence means it’s not CUI is dangerous too. The DoD has historically been inconsistent about marking documents. Just because a document doesn’t say “CUI” doesn’t mean it isn’t. Contractors must understand the categories and identify CUI even when the government hasn’t formally marked it yet.
Penalties for Getting It Wrong
Let’s talk about consequences.
An Unauthorized Disclosure (UD) — meaning CUI gets shared with someone who shouldn’t have it — is a serious matter. Depending on the category of CUI involved, the sanctions can be administrative (written reprimand, suspension), civil (lawsuits, fines), or even criminal.
For contractors, a breach can trigger the 72-hour cyber incident reporting requirement under DFARS 252.204-7012. For incidents involving CUI that touches national security, an even faster 8-hour window may apply.
Misuse of CUI — using it in a way that violates policy even without actual disclosure — is also reportable. Both misuse and unauthorized disclosures go to the DoD’s dedicated office for tracking these incidents.
Final Thoughts
DoDI 5200.48 isn’t just a bureaucratic checkbox. It’s a real-world security tool that protects sensitive government information every single day — from the desk of a Navy contractor to a military planning document traveling across a secure network.
The short answer to the exam question is easy: DoDI 5200.48.
But the real answer is much bigger. It’s a system that starts with a presidential order, flows through federal regulation, gets translated into defense policy, and ends up affecting hundreds of thousands of workers across government and industry.
Knowing it exists is the first step. Understanding how it works is what keeps you — and the country’s sensitive information — protected.
FAQs
Q1: What DOD instruction implements the DOD CUI Program?
DoDI 5200.48, titled Controlled Unclassified Information (CUI), published March 6, 2020.
Q2: Is CUI the same as classified information?
No. CUI is unclassified. It doesn’t carry labels like Confidential, Secret, or Top Secret. It’s a control, not a classification level. That distinction matters.
Q3: Who is responsible for marking CUI documents?
The authorized holder of the information at the time it’s created. If you write a document containing CUI, marking it correctly is your job right then.
Q4: What replaced “For Official Use Only” (FOUO)?
The CUI marking system replaced FOUO on new documents. Old FOUO documents don’t need to be re-marked as long as they remain within DoD control.
Q5: Can contractors decide on their own what counts as CUI?
No. Only the government can officially designate and mark CUI. Contractors use the NARA CUI Registry as a reference, but they cannot independently classify information as CUI without government direction.
Q6: What is the minimum marking required on a CUI document?
The acronym “CUI” must appear as a banner at the top and footer at the bottom of each page.
Q7: What’s the difference between CUI Basic and CUI Specified?
CUI Basic follows standard baseline rules (NIST SP 800-171). CUI Specified is governed by specific laws or regulations that impose additional or different handling requirements.
Q8: What happens if someone discloses CUI to an unauthorized person?
It’s called an Unauthorized Disclosure (UD) and must be reported. Depending on the CUI category involved, the person responsible may face administrative, civil, or criminal penalties.
Q9: Does DoDI 5200.48 apply to small businesses with DoD contracts?
Yes. If your contract includes the DFARS 252.204-7012 clause and you handle covered defense information, the full framework applies to you regardless of company size.
Q10: How must CUI be destroyed?
It must be made completely unreadable, indecipherable, and irrecoverable. For paper, cross-cut shredding. For digital media, methods consistent with NIST SP 800-88 media sanitization guidelines.
Q11: Can CUI be sent by regular email?
Only through approved, secure systems or encrypted channels. Regular personal email accounts and unsecured platforms are not approved for transmitting CUI.
Q12: What is the DoD CUI Registry?
It’s an official catalog of all CUI categories specific to the DoD. It mirrors the NARA national registry but adds DoD-specific context. Checking the registry helps you determine whether your information qualifies as CUI and which type it is.
Keep creating, innovating, and inspiring with Content Ideators every day.